Crypto security is fundamental to the safe use of cryptocurrency. There are many unscrupulous people who find it easier to steal your crypto than purchase or earn their own. The following pages will help you stay safe and better help you better understand your responsibilities as custodians of your own fortune.
How to protect your Cryptocurrency from loss and theft
| This is the fifteenth section of the Cryptocurrency and Blockchain awareness programme, How to Crypto. |
One of the biggest problems facing those of use (retail or institution) when investing in Crypto is how to protect our coins and tokens from loss (i.e. mislaid currency) or theft. We have heard (and experienced theft from banks – I once had a few thousand pounds stolen from my bank account from someone who had managed to steal my phone details. Once I knew what was going on, I contacted the bank and they ‘replaced’ the lost money within a few hours!
Now, having read through all the previous posts you are going to learn the unpalatable truth of having your crypto pie and eating it. Since we are trying to get away from banks and custodial institutions, the protections we have come to expect are not so easy to acquire. If we buy crypto, we are generally expected to be the custodians of our own money.
This is actually one of the biggest reasons that crypto is not as popular as its benefits would imply. Until we have an easy and reliable way to keep our crypto safe from loss or theft, many will be put off by investing in it. The concept ‘not your keys, not your crypto’ sounds easy enough to get your head around but crypto custodial security isn’t an easy thing to implement. People with a lot of crypto keep it in vaults with mind-bogglingly impenetrable security. People like me and you have less complex ways to store our crypto investments.
Cryptocurrency Security Soft and Hard Wallets
Crypto is usually stored in a crypto wallet. There are many available. Let’s consider the main ones:
Soft Wallets
It is common for investors who purchase currencies such as Bitcoin or Ethereum, to leave them on the central exchanges. This is considered by many to be very dangerous since such exchanges can (and have been) hacked and the money stolen. If you are going to leave your crypto on an exchange, try to see what protection they have in the form of safeguards (offline crypto storage, multi-signature security) or insurance (e.g. FDIC insurance).
If you are determined to do so however, Coinbase and Crypto.com are worthy of consideration:
 If you use the Pro version of Coinbase, trading accounts can be funded with a wide range of payment methods, including wire transfer and secure ACH transfer. It also has great security by keeping 98% of funds deposited on the platform in cold storage, so it’s impossible for hackers to steal more than 2% of users’ funds through an online attack.
If you use the Pro version of Coinbase, trading accounts can be funded with a wide range of payment methods, including wire transfer and secure ACH transfer. It also has great security by keeping 98% of funds deposited on the platform in cold storage, so it’s impossible for hackers to steal more than 2% of users’ funds through an online attack.
 Crypto.com mobile app is also a great crypto wallet. Crypto.com focused on building an app with a great ecosystem such as credit cards etc. Two factor authentication can be used as a security feature. Mobile app users can buy, sell, trade a range of interest paying currencies as well as pay with crypto. The credit card that you can load with crypto allows for a small percentage cashback (dependent on the card).
Crypto.com mobile app is also a great crypto wallet. Crypto.com focused on building an app with a great ecosystem such as credit cards etc. Two factor authentication can be used as a security feature. Mobile app users can buy, sell, trade a range of interest paying currencies as well as pay with crypto. The credit card that you can load with crypto allows for a small percentage cashback (dependent on the card).
Despite these and other facilities that eCentral Exchanes offer. Most advisors would encourage you to take your money off the Central Exchanges and put it in more secure locations with keys that are controlled by you.
There are also some very reputable mobile wallets that are becoming increasingly popular because of their ease of use. When you set up your mobile wallet, you are asked to keep a seed phrase in a secure place as this can be used to recover your wallet in case your phone is lost or stolen. Like it or not, mobiles are increasingly more secure and many don’t allow you to open your phone without a swipe key or fingerprint. The most popular mobile wallets are:
 Exodus Mobile Soft Wallet: This is a multi-currency hot wallet for Mobile Android and iOS devices. It is also free. The Desktop version also allows you to trade currencies. Exodus also supports crypto swaps for over 100 different assets. The full list of supported cryptocurrencies is available here.
Exodus Mobile Soft Wallet: This is a multi-currency hot wallet for Mobile Android and iOS devices. It is also free. The Desktop version also allows you to trade currencies. Exodus also supports crypto swaps for over 100 different assets. The full list of supported cryptocurrencies is available here.
 Metamask is, hands down, the most popular soft wallet you can get – and it’s free. I know there are lovers and haters of this wallet but in terms of popularity and ease of use, it is a winner. It is available as a mobile app and amazingly, as a Chrome browser extension! I use mine for Ethereum (ERC20) token transactions, Binance Smart Chain tokens and Avalanche ecosystem coins and tokens. It even stores NFT’s and metaverse real estate! – It’s a very versatile wallet. Alas, I don’t feel very secure using it and take the opportunity to transfer funds from it into cold storage at every opportunity. In terms of ease of use and popularity however, it’s very good. MetaMask is open-source and supported by a global community of developers and designers interested in the blockchain world.
Metamask is, hands down, the most popular soft wallet you can get – and it’s free. I know there are lovers and haters of this wallet but in terms of popularity and ease of use, it is a winner. It is available as a mobile app and amazingly, as a Chrome browser extension! I use mine for Ethereum (ERC20) token transactions, Binance Smart Chain tokens and Avalanche ecosystem coins and tokens. It even stores NFT’s and metaverse real estate! – It’s a very versatile wallet. Alas, I don’t feel very secure using it and take the opportunity to transfer funds from it into cold storage at every opportunity. In terms of ease of use and popularity however, it’s very good. MetaMask is open-source and supported by a global community of developers and designers interested in the blockchain world.
Hard Wallets
Also known as “physical” or “cold” wallets, they look like USB drives and act as a physical storage device for tokens and coins. All hardware wallets have a private key: A password-like code that allows you to decrypt the wallet and access its stored coins or tokens. Most don’t allow you to see the private key as this would cause issues with security. Basically, you need to have the device physically available for you to withdraw funds. Each hardware wallet comes with a seed phrase that you can keep safe (and secret). The seed phrase can be used to get back your crypto in case the hardware wallet is lost or stolen.
At this point, I need to re-explain that all crypto coins and token transactions are stored on the blockchain of their respective networks. Bitcoin transactions are stored on the bitcoin blockchain and your coins are validated on that chain. They aren’t physical and are never actually stored in the wallet. They are simply associated with that wallet. The coins are actually on the blockchain so if you lose your wallet, as long as you can retrieve your private key, you can still get back your coins. If your seed phrase is stolen, the thief will be able to create a different wallet and steal your coins and tokens. Always keep your seed phrase in the most secure place you know of. Protect it against fire, teft and loss. Some people put them in safety deposit boxes – NEVER in emails or in their hard drives as these are not considered secure by today’s standards.
Currently, the top three crypto hardware wallets are:
Ledger Nano X
The Ledger Nano X and is the best hardware wallet in the market. It’s a widely-used hardware USB device that is roughly the size of a small flash drive, measuring at 72mm × 18.6mm × 11.75mm (2.83 x 0.73 x 0.46 inches) and weighing in at 34g.

Feature: Picture courtesy of Crypto News Flash
There is a less expensive and less full featured version called the Nano S. The Nano X has a Bluetooth facility that allows you to use it with your phone or laptop without the need of a wired connection. Its battery time allows 8 hour standby mode. The most important difference between the two versions is that the Nano X can hold many more currencies than the cheaper version. The ‘S’ is a third of the price but is unable to hold a large number of currencies.
I personally don’t like using The Ledger Nano. It’s fiddly, tricky and time consuming. The software isn’t particularly slick and the little window on the front is cheap and nasty. Nevertheless it is widely regarded as the best hardware crypto wallet money can buy and is reliable. The app (for desktop and mobile) is very good and very easy to use.
Trezor Model T:
The Trezor Model T is much easier to use and as soon as you plug it in, it’s ready to use. It can be used with Android devices through apps such as the Trezor, Mycelium, and Multibit HD wallets. This minimises the risk of private key discovery, even if the PC is infected by malware.
There is a PIN system in Trezor which discourages 9and certainly prevents brute-force hacking attempts. After each incorrect guess at entering a pin, the waiting time between guesses is doubled. Making 30 wrong guesses will take over 15 years!

Feature: Picture courtesy of buybitcoinworldwide.com
The setup (seed) phrase is 24 words like the ledger. The seed is generated offline and displayed on the wallet’s screen, which ensures that the seed phrase is never on an internet-connected device. You can of course, recover your wallet with the seed phrase so it is always important to keep it safe and secure. I’ve not used one but I’ve seen some reviews and these suggest that the purchase of the cheaper Model One (with a smaller black and white screen) is more cost effective.
Ellipal Titan
This is a relative newcomer to the crypto hardware wallet market but it’s features make it very much worth considering. The device is a standalone unit which looks and feels like a small mobile phone, measuring at 118 x 66 x 9.7mm with an LCD screen measuring 108mm. It’s resistant to most forms of physical abuse and IP65 rated dust proof and water proof.
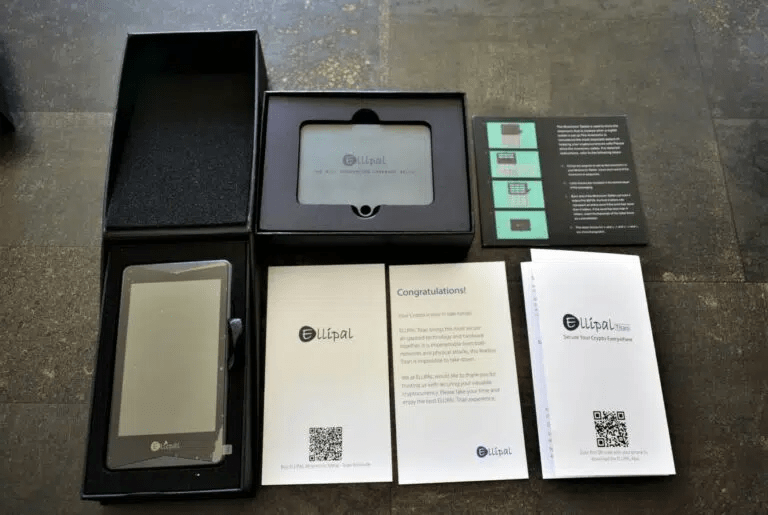
Feature: Picture courtesy of CoinBureau
This is reputed to be one of the most secure air-gapped hardware wallets. The device itself does not connect to the internet and is built with no online components or ports, which means it is protected from remote online attacks.
It has a universal OCCW (Open Cross Chain Wallet) Protocol which allows for multi wallet support. It will also auto wipe all your data if it detects any breach and can be restored on another device by using the 12 word seed phrase.
Paper wallets
These are a particular type of online wallet generated by web platforms such as BitAddress or WalletGenerator. These applications create Bitcoin addresses and private keys that can then be printed out. Innovations such as the use of the QR code makes use much easier.

These are particularly useful if you are worried about long term storage and the updates required for the devices (seemingly every few weeks). If you have a secure and safe p;lace to store something long term, this can be a very cheap and easy solution.
So there you have it, a brief overview of security options for your crypto. It’s worth pointing out that you should not discuss your crypto holdings with people. if i was a rich person (fiat currency or crypto) I wouldn’t go around telling anyone how much I had. it’s not just being careful about the devices you use to store your crypto, it’s about being discreet about what you hold and where.
We are in complete control of our crypto currency if we want to be. Alas, that responsibility has meant that millions of crypto coins worth billions of dollars have been lost through poor management (literally lost the keys), theft and extortion. Custodial crypto security is and always should be, our responsibility.
This section completes the How to Crypto Awareness course. There is a very useful Glossary of Terms that you should checkout. This has all the usual words common to the cryptocurrency vocabulary. The How to Crypto Bibliography is a great section for getting more (in particular, more detailed) information about the topics covered in this awareness course. It has links to documents, video and other resources that you will find useful when researching interesting cryptocurrency projects.
This article is copyright 2022 by Tony Fawl, CryptoNET.
This page is part of the How to Crypto Web Series, an awareness course for beginners interested in blockchain projects and cryptocurrency investment. Please checkout the Bibliography and Glossary of Terms pages for other useful resources and links. To find out what we do, take a look at the About Us page.
Disclaimer: CryptoNET.org.uk is not a registered investment, legal or tax advisor or a broker or dealer. All investment/financial opinions expressed by CryptoNET.org.uk are from the personal experiences of the owner of the website and are intended as educational and entertainment material. Best efforts are made to ensure that all information is accurate and up to date but we would still recommend that you do your own research before making investment decisions.
If you have found this page useful, please consider a small donation to help fund the site:
[crypto-donation-box]
Thank you.


Comments are closed.